February 12, 2026
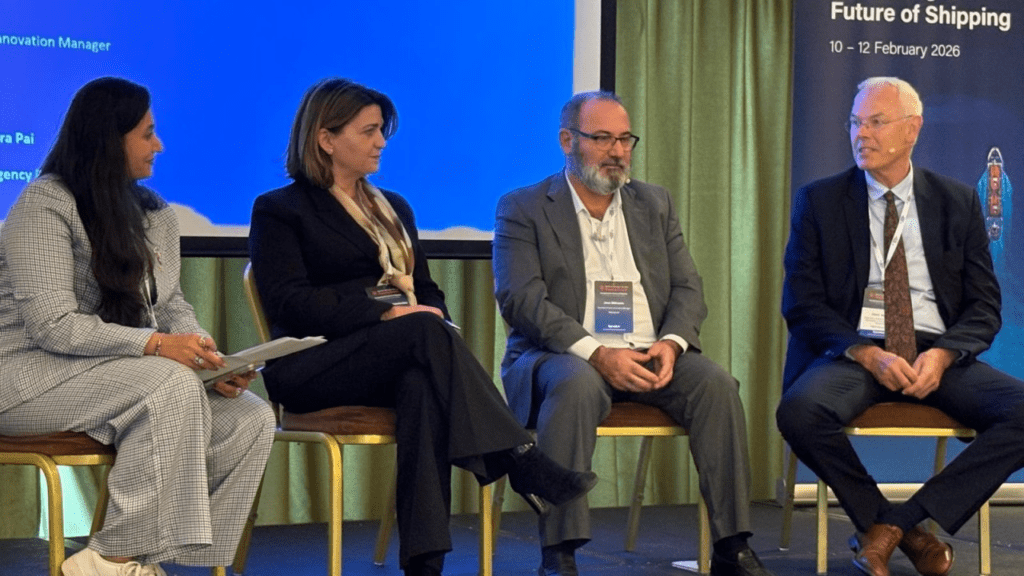
At the Maritime Information Services Shipping Summit in Athens, the final session of day one focused on a topic that surfaced repeatedly throughout the event: cyber security in the maritime sector. The panel discussion “From bridge to boardroom” brought together four complementary perspectives — regulatory and legal, operational from a shipowner’s standpoint, and behavioral from the human factor.
Moderated by Dr. Akanksha Batura Pai (Executive Director, Sinoda Shipping Agency), the conversation delivered a clear message: cyber security is not just an IT matter. It is an organisational challenge that touches leadership, culture, training, and resilience.
“It won’t happen to us” is a dangerous assumption
Dr. Iliana Christodoulou Varotsi a Christodoulou Varotsi (Academic Course Director, Lloyd’s Maritime Academy) opened by addressing a persistent myth: that cyber security is primarily an IT issue. Equally risky, she noted, is the belief that an organisation is “too small” or “not visible enough” to become a target.
Attackers, she emphasised, do not pursue visibility — they pursue value. Data, operational processes, supply chain access, and system entry points are attractive regardless of brand recognition. As a result, cyber resilience requires a holistic approach involving ownership, governance, procedures, people, and technology.
From compliance to real resilience
Jose Milhazes (Business Process Innovation Manager, GasLog) offered the shipowner perspective. His advice was direct: assume it will happen. Not to create fear, but to ensure organisations structure their response accordingly.
Milhazes described how boardroom priorities shift from compliance checklists to resilience once cyber risk is connected to reputation, financial exposure, and operational continuity. In practice, this means regular reporting to senior management — including attack volumes, incident levels, threat classifications, and employee training coverage.
Strikingly, his examples were not about complex technical solutions but about behaviour and habits. A lesson drawn from a personal incident — a home burglary enabled by information shared on social media — translated into a practical policy message for seafarers: avoid sharing photos of vessels, equipment, and operations online. He also highlighted simple, low-disruption measures such as security reminders on locked screens and behavioural nudges encouraging employees to secure their devices. Small interventions, significant impact.
“Hello, I’m Albert, and I’m addicted to AI”
Albert Mulder (Human Behaviour Specialist Maritime Industry, WE EmpowerAI) brought the discussion to one of the sector’s newest challenges: artificial intelligence. Beginning with humour but ending with urgency, he described how AI is rapidly evolving from chat tools into agent-based systems capable of acting independently, communicating, and executing transactions. This turns “Shadow AI” into a broader organisational risk rather than simply employees experimenting with ChatGPT.
Mulder identified two misconceptions undermining cyber readiness. The first is the cliché that “people are the weakest link.” Sometimes true, he acknowledged, but more often the issue lies in the system: unclear procedures, missing frameworks, and the absence of safe alternatives push employees into risky behaviour. The second misconception is the belief there is still time to react. According to Mulder, there is not. The speed of AI adoption, combined with open-source availability and low barriers to use, requires immediate action.
His behavioural insight was clear: humans are excellent problem solvers seeking efficiency, but poor risk assessors. Employees will adopt tools that help them perform better, even when risks are not fully understood. Therefore, the solution is not prohibition or lengthy policies but a systemic approach combining clear frameworks, training, and practical alternatives.
Regulation exists — implementation is the real challenge
From the legal perspective, Varotsi stressed there is no single instrument that solves cyber risk. The international foundation lies in IMO instruments, notably the integration of cyber risk management into the Safety Management System context, supported by industry guidelines and best practices.
She referenced class notations, ISO and NIST frameworks, and regional guidance, including ENISA, the EU cyber security agency, which has issued port-level guidance. Regionally, she highlighted NIS2, which identifies “water transport” as an essential sector. Depending on services and organisational scale, companies within the maritime ecosystem may fall within its scope.
Her key message: the framework is robust, but effectiveness depends on implementation. Resilience is not only about protection — it is about withstanding, responding, and recovering. Training and demonstrated competence are therefore not optional but part of duty of care.
From knowledge to behaviour: drills and simulations
The discussion then shifted from policy to practice. Mulder explained that cyber resilience should not be measured in knowledge or awareness alone, but in behaviour. Just as organisations conduct fire drills and abandon-ship drills, they must introduce cyber drills — both announced and unannounced. Examples include phishing simulations, social pressure scenarios, USB device tests, and data-sharing situations.
Across the panel, a common theme emerged: cyber security is safety. It is not an additional activity but a prerequisite for safe operations.
Final takeaway: start now and organise it properly
In closing, Dr. Batura Pai asked each panelist for one practical action. Mulder advised organisations to begin using AI immediately — but safely and responsibly — while providing employees with approved tools and a framework. Milhazes recommended embedding cyber security into every digitalisation investment and questioning suppliers accordingly. Varotsi emphasised awareness, training, guidance, and common sense.
The shared conclusion: the industry cannot rely on reactive policies. Achieving cyber resilience requires leadership, organisation-wide ownership, and continuous professional development — from bridge to boardroom.





